We recently learned that Windows VPN users that rely on Google Chrome and Firefox could be in danger of having their IP address revealed. Regardless of whether or not you’re connected to a VPN server. The WebRTC vulnerability allows sites to log your VPN IP address along with your real IP address.
Mac and Linux users are not impacted by the WebRTC security flaw. It only applies to Windows users running Firefox and Chrome. Luckily there are already fixes out for both web browsers. Here’s a quick guide to fixing the WebRTC vulnerability so you can avoid any future IP leaks while connected to VPN.
WebRTC IP Leak Fix in Firefox
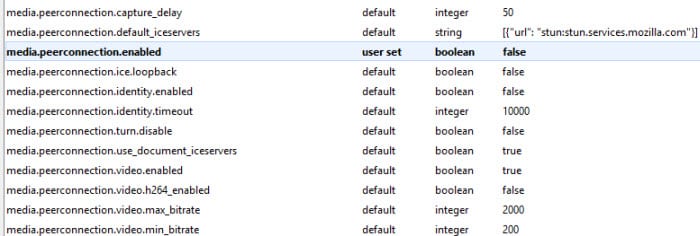
Firefox users have two choices to take care of the IP leak issue. The first is to install the NoScript addon. If you’d rather not install the addon you can also make a manual change in the web browser. To do so type “about:config” into the address bar and press enter. Next click on the “I’ll be careful, I promise” button. From there you can fix the problem by double clicking the “media.peerconnection.enabled” entry. That will set it to false. You are now protected from the WebRTC security flaw.
WebRTC IP Leak Fix in Chrome
Google chrome users have two choices as well. You can either install the new WebRTC Block extension or ScriptSafe. Either option will help you fix the WebRTC IP leak issue on Chrome.

I hope you found out guide useful in helping fix the WebRTC IP leak security flaw in Chrome and Firefox. Internet Explorer users are not impacted by the issue. You can use the following site to test for IP leaks:
If you’d like to learn more about the vulnerability and impact on users over time here are some additional resources:
Following us @VPNFan for the latest security and VPN news.
