 Mullvad VPN is an Internet privacy service started in 2008 and offered by the Swedish company Amagicom AB. Like most VPNs, Mullvad hides your IP address and provides you with a shared virtual IP. Mullvad does not keep any logs of your Internet activities and encourages anonymous payment methods like Bitcoin. Their service generates a unique “16 digit number” that is used to create and manage your account. It is also used to provide login credentials to their apps and network. Mullvad does not require any personal information to use their service. Consequently, it is one of the most privacy conscious VPNs that we have reviewed.
Mullvad VPN is an Internet privacy service started in 2008 and offered by the Swedish company Amagicom AB. Like most VPNs, Mullvad hides your IP address and provides you with a shared virtual IP. Mullvad does not keep any logs of your Internet activities and encourages anonymous payment methods like Bitcoin. Their service generates a unique “16 digit number” that is used to create and manage your account. It is also used to provide login credentials to their apps and network. Mullvad does not require any personal information to use their service. Consequently, it is one of the most privacy conscious VPNs that we have reviewed.
Mullvad employs some of the best security protocols and algorithms, including OpenVPN (AES-256) and what many see as its “heir apparent”, WireGuard. Therefore, if you are primarily looking for a VPN to secure your Internet traffic and protect you online identity, Mullvad is a good choice.
Mullvad Pricing and Payment Options
Mullvad has a very simple marketing strategy. They offer a single, all-inclusive plan. In the past you could sign up for 1 to 12 months of service. However, Mullvad has decided to offer a flat rate of €5 a month. You can still top off your account with as much credit as you want but the price is the same regardless. Mullvad generates a unique “16 digit” registration number when you create an account. Note that in the past Mullvad offered a 3 hour free trial but that promotion has ended.
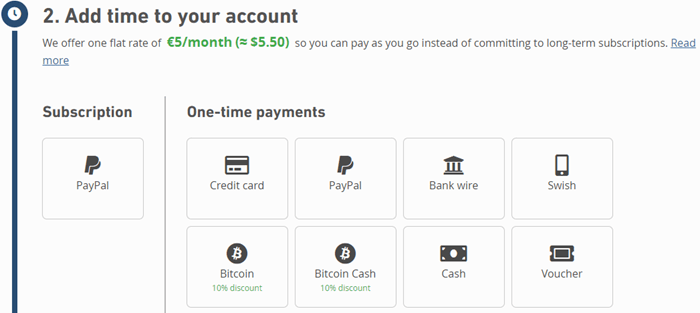
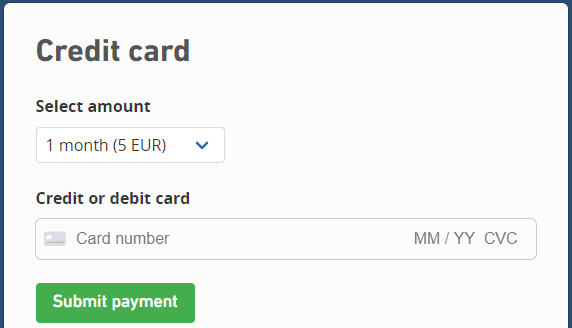
The payment options that Mullvad accepts include credit card, PayPal, and Swish. To pay by credit card, click on the payment button. This will take you to another page where you can complete your transaction. You will only have to enter the amount of time you want to add and credit card number along with its expiration date and verification number. Credit card transactions are handled through the Stripe payment platform.
If you like to keep all of your online transactions in a central place, Mullvad accepts PayPal. You will need a Swedish phone number to pay using the Swedish mobile payment platform Swish. You can pay by cash by sending it along with your account registration number to the Amagicom AB address found in the footer of their website. If anonymity is your goal, they accept both Bitcoin and Bitcoin Cash. Additional cyptocurrency payments receive a 10% discount due to lower fees and less administration. Finally they accept bank transfers and activation vouchers purchased in retail locations.
Mullvad VPN Service Features
Mullvad customers have access to all service features which include the following:
- VPN network – that consists of 37 countries and about 60 locations worldwide.
- Servers – that consists of OpenVPN, WireGuard, and bridge servers.
- Muti-device support – for Linux, Mac OS, iOS, and Android.
- Internet traffic – is encrypted using OpenVPN AES-256-GCM.
- Protocol – support for only the most secure high performance VPN protocols: OpenVPN and Wireguard.
- Multiport – OpenVPN access that includes Port 53: UDP (DNS); Prot 80: TCP (HTTP); Port 443: TCP (HTTPS) as well as others.
- Port forwarding – to allow external hosts to access your local network.
- P2P – is not blocked.
- Mullvad VPN – runs in-house public key infrastructure (PKI).
- Five simultaneous connections – via one account.
- Anonymous digital – accounts that do not require any personal information
- Anonymous payments – by means of cryptocurrencies.
About Mullvad and Amagicom AB
As was previously mentioned, Mullvad was created in 2008 by the Swedish company Amagicom AB. Unlike some VPNs which hide their decision makers, it does not. A simple search reveals that the service is controlled and operated by its CEO Jan Jonsson, along with input from co-founders, Fredrik Strömberg and Daniel Berntsson. Mullvad was created to realize their goal “to make Internet censorship and mass surveillance completely ineffective” and guard everyone’s “universal right” to privacy.
In August of 2016 Mullvad completed a major upgrade of its server infrastructure that doubled its capacity. It also increased the security of their servers in Sweden and the Netherlands (Amsterdam). This was acomplished with the help of data center specialist 31173 Services which provided high performance servers focused on security. This was to be the first of a series of major investments to improve the VPN service according to CEO, Jan Jonsson.
February of 2017 provided another of these advancements which increased regional connectivity by adding more server locations in the United States, Sweden, and Canada. This gave Mullvad users three locations in Sweden (Stockholm, Malmö, and Helsingborg), two locations in Canada (Ontario, and British Columbia), and new U.S. servers in Buffalo, New York. Thus giving customers more localized options ensuring faster connections from within their home countries. It was also announced that more region-specific locations would be rolled out in the future.
Mullvad then signed a partnership with Eurosecure, distributor of ESET antivirus software products in Scandinavia in March of 2017. This allowed Mullvad to be sold throughout the Nordic region in shops and online stores along with ESET products as part of its rapid expansion goals. They packaged their VPN service in ESET’s recognizable boxes. Each includes its own anonymous activation code to be used with Mullvad accounts. Mullvad and ESET are perfect retail partners as neither save any information about their customers.
Working with 31173 Services AB in October of 2017, as part of its rapid expansion and continued efforts to improve its infrastructure, Mullvad established a 10-Gbit connection to one of the world’s largest internet exchange points (Amsterdam). This allowed it to peer with 800 other international networks. Public peering through this exchange lets Mullvad send traffic directly to one another. Bypassing the longer public Internet routes allows its VPN network to improve performance, provide more redundancy, and decrease network latency. At the same time, Mullvad doubled its server capacity in both Stockholm and Amsterdam.
In September of 2018, and independent audit of eight testers from Cure53 and Assured was conducted. This audit took a total of 18 days to complete. It highlighted a total of seven issues. None of these were remotely exploitable. Of the seven vulnerabilities found, two required local access to the computer. Five were miscellaneous issues. Of these, three required local access, one pertained to the Mullvad website, and the last one reflected on software dependencies. Mullvad has fixed three of these in its latest release (2018.3) and is looking into the others.
Mullvad VPN Servers and Network
As you can see from the previous section, Mullvad has recently undertaken some major projects to upgrade both the security and performance of their VPN network. As a result, their current network consist of about 65 locations in 38 different countries. These are strategically placed in Asia, Europe, North America, South America, and Oceania to allow their service to provide the customers maximum performance worldwide. Their network only supports connections using the OpenVPN and WireGuard protocols. They also furnish obfuscation servers for those who need it to overcome censorship, bypass online blocking, and avoid ISP throttling of their Internet experience.
Mulvad Server Locations
The Mullvad infrastructure is composed of three different types of servers: OpenVPN, WireGuard, and bridge servers. Their network currently has about 260 OpenVPN severs, 48 WireGuard servers and 6 bridge servers. Mullvad uses only physical servers (no virtual servers) for maximum security. You can find out additional information about all of their servers on the server page of their website. They own their servers in both Sweden and the Netherlands. Additionally, they rent servers which are not shared with other clients from selected providers in Canada, Germany, Singapore, and the United States. Thus your Internet traffic will be delivered by Tier 1 and Tier 2 carriers when using their VPN network.
Mullvad OpenVPN Servers
- Their OpenVPN servers locations – country (city) are:
- Asia
- Hong Kong (Hong Kong); Israel (Petach-Tikva); Japan (Tokyo); Singapore (Singapore);
- Europe
- Austria (Wien); Belgium (Brussels); Bulgaria (Sofia); Czech Republic (Prague); Denmark (Copenhagen); Finland (Helsinki); France (Paris);
- Germany (Berlin, Frankfurt);
- Hungary (Budapest); Italy (Milan); Luxembourg (Luxembourg); Netherlands (Amsterdam); Norway (Oslo); Poland (Warsaw); Portugal (Lisbon); Romania (Bucharest); Serbia (Nis); Slovakia (Bratislava); Spain (Madrid);
- Sweden (Gothenburg, Helsingborg, Malmö, Stockholm);
- Switzerland (Zurich);
- UK (London, Manchester);
- Ukraine (Kiev)
- North America
- Canada (Montreal, Toronto, Vancouver);
- USA (Atlanta, GA; Boston, MA; Charlotte, NC; Chicago, IL; Cleveland, OH; Dallas, TX; Denver, CO; Las Vegas, NV; Los Angeles, CA; Miami, FL; New York, NY; Newark, NJ; Oklahoma City, OK; Philadelphia, PA; Phoenix, AZ; Piscataway, NJ; Richmond, VA; Salt Lake City, UT; San Francisco, CA; San Jose, CA; Seattle, WA; Secaucus, NJ; Washington, DC)
- South America
- Brazil
- Oceania
- Australia (Brisbane, Melbourne, Perth, Sydney)
- Asia
Mullvad WireGuard Servers
- Their WireGuard servers locations are as follows: country (city)
- Asia
- Hong Kong (Hong Kong); Japan (Tokyo); Singapore (Singapore);
- Europe
- Austria (Wien); Belgium (Brussels); Bulgaria (Sofia); Czech Republic (Prague); Denmark (Copenhagen); Finland (Helsinki); France (Paris);
- Germany (Berlin, Frankfurt); Italy (Milan); Netherlands (Amsterdam); Norway (Oslo); Poland (Warsaw); Romania (Bucharest); Slovakia (Bratislava); Spain (Madrid);
- Sweden (Gothenburg, Malmö, Stockholm); Switzerland (Zurich);
- UK (London, Manchester);
- North America
- Canada (Toronto, Vancouver);
- USA (Atlanta, GA; Chicago, IL; Dallas, TX; Denver, CO; Las Vegas, NV; Los Angeles, CA; Miami, FL; New York, NY; Newark, NJ; Phoenix, AZ; Salt Lake City, Seattle, WA)
- Oceania
- Australia (Sydney)
- Asia
Mullvad Bridge Servers
If you’re stuck behind a restrictive firewall and are unable to access Mullvad VPN servers directly, you can try connecting to one of their bridge servers. These servers are in the following locations: the Netherlands (Amsterdam); Norway (Oslo); Sweden (Helsingborg, Malmö); USA (Los Angeles, CA). You can connect to these in a variety of ways: Shadowsocks method, SSH method, Stunnel method.
You can also use these to create multi-hop connections by connecting to one location and exiting through another. This can help increase your anonymity and privacy but comes at a performance cost. If you want to know more about using these, Mullvad has guides on their website to walk you through bridge connections and usage.
Qubes: Mullvad Server OS
Additionally, Mullvad servers run the high security, open source Qubes operating system. Qubes takes an approach called security by compartmentalization. Each of these different compartments, which are called “qubes”, have their own isolated security. This approach lets you keep the different things: file management, email, administration, etc. securely separated from each other. Therefore, if one of these isolated qubes is compromised, it will not affect the others.
For example, you might use one qube for visiting untrusted websites and another for online banking transactions. If your untrusted browsing qube gets compromised by a malware-laden website, your online banking activities will not be at risk. Additionally, the OS supports the creation of single use disposable qubes. Thus if you are concerned about malicious email attachments, Qubes will allow you to open every attachment in its own single-use disposable qube. In this way, Qubes permits you to do everything on the same physical computer without having to worry about a single successful cyber attack taking down your entire system.
Moreover, all of these isolated qubes are integrated into a single, usable system. Although programs are isolated in their own separate qubes, they are displayed in a single, unified desktop environment. Furthermore in Windows, each qube’s (window) is framed with a unique colored border so that you can easily identify windows from different security levels. The OS includes an integrated file and clipboard that allows you to copy and paste between security windows. The difference being that you have to make these transfers manually at the physical machine. It also separates the hardware security from its functional security and separates software installation from software use by allowing it to share a common root file system. You can find additional information here.
Mullvad User Privacy
Although located in Sweden which is a “14 Eyes” country Mullvad believes in protecting their users privacy. This protection starts when you first create an account for their service. Unlike other VPN services that we have reviewed, creating an account requires no personal information from you. Instead, registration generates a unique 16-digit number that is used to manage your account and connect to the Mullvad network. It also provides 3 hours of free access to test the service. After 3 hours you will need to add time to your account to continue using their VPN service. Mullvad states this as follows in their Privacy Policy.
Our anonymous, numbered accounts
We want you to remain anonymous. When you sign up for Mullvad, we do not ask for any personal information – no username, no password, no email address. Instead, a random account number is generated, a so-called numbered account. This number is the only identifier a person needs in order to use a Mullvad account. This is a fundamental difference that sets us apart from most other services.
Anyone at anytime can create as many numbered accounts as they wish on our website. An account can be used by multiple people or by someone other than the person who initially generated it. A Mullvad account has two properties: the account number and the time remaining on that account. When an account is created, it comes loaded with three hours to try Mullvad for free. At once the countdown starts. After those three hours have passed, the account has no time left. Using it to connect to Mullvad is no longer possible unless it is loaded with more time.
Mullvad Collects No Logs
In addition to using anonymous numbered accounts, Mullvad does not store any activity logs for the VPN users. This includes Internet traffic, DNS requests, IP addresses, timestamps, individual user bandwidth, or any other account activity. They are a true no-log service when it comes to personal VPN use. An excerpt from their Privacy Policy states this as follows:
What we don’t log
We log nothing whatsoever that can be connected to a numbered account’s activity:
• has no logging of traffic
• no logging of DNS requests
• have no logging of connections, including when one is made, when it disconnects, for how long, or any kind of timestamp
• no logging of IP addresses
• no logging of user bandwidth
• has no logging of account activity except total simultaneous connections …
Information Mullvad Collects
Mullvad only collects some aggregated server data to facilitate the normal operation of their VPN service. The only individual information that they look at is the real-time number of simultaneous connections on an account. They keep up with this using your randomly generated account number but it is not saved. Here is an excerpt from their Privacy Policy showing exactly what is kept.
Our VPN servers send three types of data to our monitoring system:
• total number of current connections
• CPU load per core
• total bandwidth used per server.
We log the total sum of each of these statistics in order to monitor the health of each individual VPN server. We ensure that the system isn’t overloaded, and we monitor the servers for potential attacks, bugs, and network issues.
Additional Privacy and Anonymity
In addition to these ways that Mullvad protects your privacy, it also allows you to pay using anonymous methods like cash, Bitcoin, and cryptocash. Their service provides protection against DNS, IPV4 and IPv6 leaks.
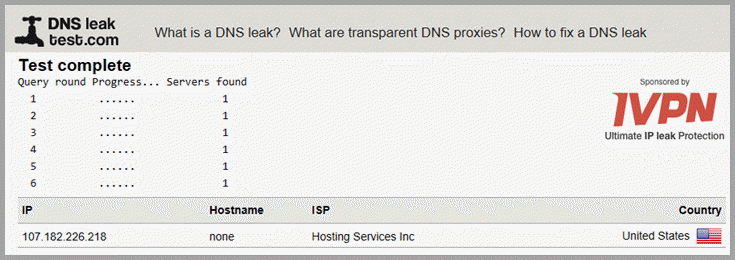
This was borne out by our own DNS leak testing. Dependent on your payment method, some personal information may be kept by payment processors.
Privacy Summary
As you can see, Mullvad takes your privacy very seriously. As a matter of fact, they are one of the most privacy oriented VPN services that we have yet reviewed. Consequently, you can be assured that your privacy and anonymity will be guarded while connecting to their VPN service. However as always, you should examine their TOS and Privacy Policy for yourself.
Mullvad VPN Service Security
Default App Protocols Cryptography
Mulvad only allows connections by either OpenVPN or the new WireGuard VPN protocols. OpenVPN is widely believed to be the best performing VPN protocol available today. If implemented correctly, it can provide maximum Internet traffic security, as well as, fast speeds. Mullvad can be used on Windows, macOS, Linux, iOS, Android, and most other devices supporting OpenVPN. Additionally, Android users can connect to the service using WireGuard. It should be noted that this protocol is in its beta phase and still under development despite its great promise.
Default Encryption Used By Mullvad
Mullvad OpenVPN
To evaluate the security of the encryption used by the Mullvad VPN service, we need to look at its default implementation in their OpenVPN software app.
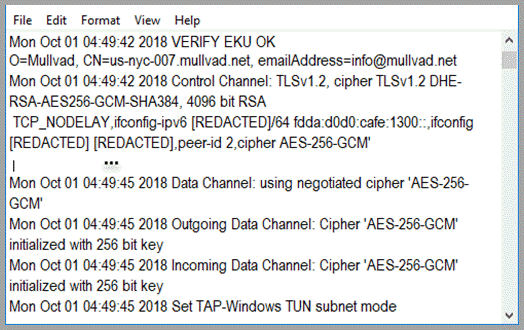
From their connection log file and other sources we find that their OpenVPN connections uses the following:
- Handshake (server/client ) – is by RSA-4096 with 1024 bit Diffie Hellmann keys.
- Data channel cipher – is AES-256-CBC.
- Data authentication – uses HMAC SHA256.
- Control channel cipher – is AES-256-GCM.
- Control channel authentication – uses SHA-384.
Given these parameters, it is clear that Mullvad has implemented some of the best encryption algorithms into their VPN service. They use RSA-4096-DHE with SHA-384 for initiation and authentication of the server and client. Keys are renegotiated every 60 seconds for increased forward secrecy protection. Your data is secured using an encryption level that is equivalent to that applied to “Secret” documents by the United States government.
Alternate Android WireGuard Security
Mullvad has also implemented WireGuard as an alternate VPN structure. WireGuard is a new open-source type of secure network tunnel (VPN) that was developed by Jason A. Donenfeld in 2015. In late July of 2018, he submitted a proposed set of patches ( ) to the Linux kernel project to integrate the secure VPN tunnel software as an official network driver. Linus Torvalds, the creator of the Linux kernel recently stated the following regarding this.
Can I just once again state my love for it and hope it gets merged
soon? Maybe the code isn’t perfect, but I’ve skimmed it, and compared
to the horrors that are OpenVPN and IPSec, it’s a work of art.
Originally released as an optional add-on module for Linux and now available for Android, macOS, Windows, and other platforms , its integration into the Linux kernel is currently under review by code maintainers.
WireGuard aims to be simpler to set up and maintain than other VPN implementations like IPSec and OpenVPN+OpenSSL while still providing the highest degree of security and privacy. These objectives are meant to be achieved by using the latest “state-of-the-art” non-agile cryptography that is designed to operate at the network level and maintaining a smaller code base. At about 4000 lines of open-source code, Wireguard has the potential to be easier to implement and audit than its competition.
The following are the protocols and cryptographic primitives currently used by WireGuard:
- ChaCha20 for symmetric encryption, authenticated with Poly1305, using RFC7539’s AEAD construction
- Curve25519 for ECDH
- BLAKE2s for hashing and keyed hashing, described in RFC7693
- SipHash24 for hashtable keys
- HKDF for key derivation, as described in RFC5869
WireGuard is designed without cryptographic agility and instead uses crypto-versioning. This means that its cryptography is taken as a whole rather than as individual primitives. This means if a primitive is compromised, not only is it replaced but a new total Wireguard cryptography is created and a new version is released. Thus peers need only negotiate the WireGuard version and not individual protocols and primitives.
Additionally by using these high-speed algorithms and the fact that WireGuard resides in the kernel or core of the OS, it has the potential to be very high-speed with nearly instantaneous connections. This increases its scalability. Thus it can be used on everything from embedded interfaces, smartphones, and supercomputers to backbone routers.
Cryptokey Routing
At the heart of the WireGuard secure tunnel is a simple idea called “Cryptokey Routing”. This operates by generating public and private encryption keys. These public keys are then associated with a list of IP addresses which are allowed to use the VPN tunnel and its associated destination. Thus, the list of allowed IP addresses acts like a routing table when sending packets, and as a control list when receiving them. WireGuard calls this a “Cryptokey Routing Table”. This table simply associates these public encryption keys and their allowed IP addresses.
Each WireGuard network interface consists of a unique private key and a list of allowed peers. All peers have short public keys. These are used to authenticate each other. Configuration files or other common distribution methods are used to distribute these keys. WireGuard describes this process as follows.
WireGuard associates tunnel IP addresses with public keys and remote endpoints. When the interface sends a packet to a peer, it does the following:
- This packet is meant for 192.168.30.8. Which peer is that? Let me look… Okay, it’s for peer ABCDEFGH. (Or if it’s not for any configured peer, drop the packet.)
- Encrypt entire IP packet using peer ABCDEFGH’s public key.
- What is the remote endpoint of peer ABCDEFGH? Let me look… Okay, the endpoint is UDP port 53133 on host 216.58.211.110.
- Send encrypted bytes from step 2 over the Internet to 216.58.211.110:53133 using UDP.
When the interface receives a packet, this happens:
- I just got a packet from UDP port 7361 on host 98.139.183.24. Let’s decrypt it!
- It decrypted and authenticated properly for peer LMNOPQRS. Okay, let’s remember that peer LMNOPQRS’s most recent Internet endpoint is 98.139.183.24:7361 using UDP.
- Once decrypted, the plain-text packet is from 192.168.43.89. Is peer LMNOPQRS allowed to be sending us packets as 192.168.43.89?
- If so, accept the packet on the interface. If not, drop it.
All of the technical details (IP hiding, authenticity, perfect forward secrecy, protection against attack, cryptography, etc.) needed to establish your Internet privacy and security using WireGuard happen behind the scenes. From a users standpoint, once WireGuard is installed and configured, it requires only a tap on its toggle to turn a tunnel on or off. We will examine this in greater detail when we examine the Mullvad for Android implementation.
Mullvad Security Summary
Mullvad uses OpenVPN as its default primary connection protocol along with AES-256 data encryption. This provides a high level of security for your Internet traffic. Initial handshake uses RSA-4096 with 1024 DH keys to provide authentication and avoid MitM attacks. They implement forward secrecy to limit the exposure of users online data. Mullvad has a kill switch to help protect your traffic from unplanned VPN service disconnects. Their app guards against DNS leaks. At the same time they are examining new technologies to protect you in the future. Therefore, we think that your Internet traffic should be well secured when using the Mullvad VPN service.
Mullvad Support
The Mullvad support is through email. They recommend that you use encrypted email to correspond with them if you are including personal information. This support is available only during normal operating hours of their Sweden headquarters. General questions may be answered quickly (within a couple of hours). More technical ones may take longer.
Additionally, Mullvad has a FAQ database that includes general VPN issues, payment and subscription information, security concerns and other issues. They also have a guide section on their website that will help you with many connection problems. Finally, you can follow them on Twitter and Facebook.
Mullvad VPN Service: Hands-On
Mullvad has an app which will run on the following environments:
- Windows 7 and above
- Mac OS X Mavericks (10.9)
- Linux distributions such as Debian, Ubuntu, and Fedora
They also support OpenVPN and WireGuard installations and configuration files for any devices that support them. Information on these can be found on the guides section of their website.
Creating a Mullvad VPN Account
Before you can use the Mullvad service, you first have to create a new account. This is easy to do. First open their website in your browser and click on the “Get account” button. It is at the top of the screen in the website main menu. This will open the account creation screen.
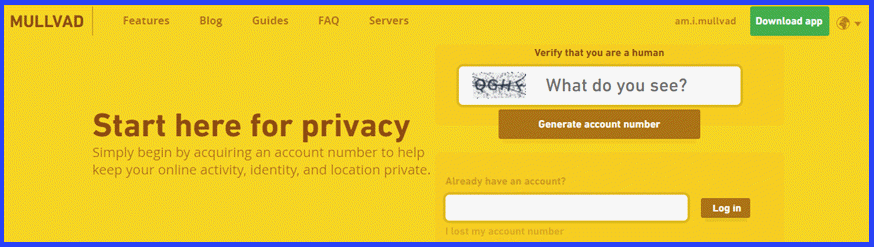
First, you need to verify that you are human by selecting the Captcha box and typing in the letters shown. Next, select the “Generate account number” button. This will open a screen welcoming you to the Mullvad VPN service. It also displays the random “16 digit” number generated for your account. This number will be used to authenticate you with their service. You will also use it to control and manage your Mullvad account.
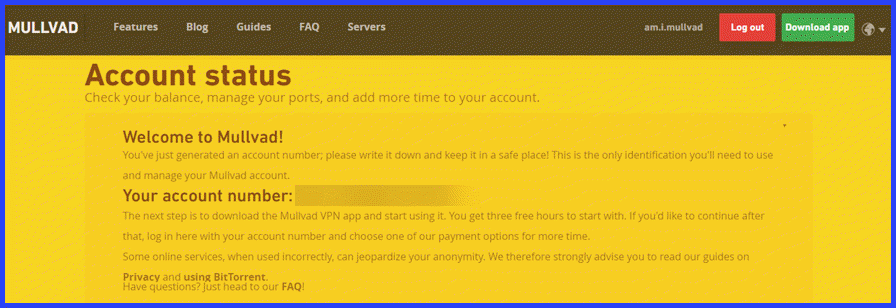
In addition, it informs you that you need to download the application software for your device and that you will receive three free hours of service on their VPN network. Subsequent logins will open a page similar to this.
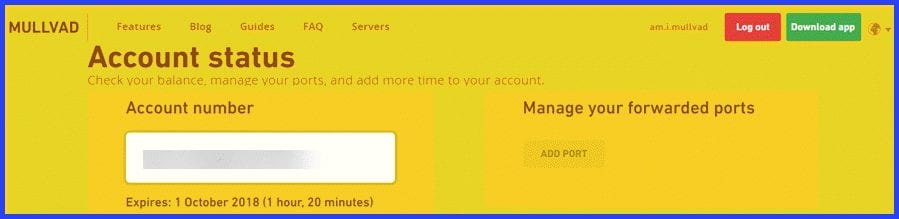
You can check your account balance, set up port forwarding, and manage your account from here. You can also click on the “Download app” button to install the client software to your computer.
Hands On: Mullvad Windows Client
Installing the Mullvad Windows Client
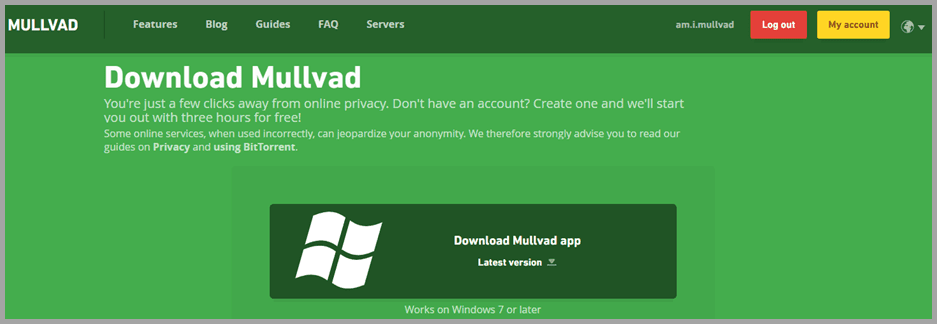
Click on the “Download app” button to open the page that will allow you to download the app for Windows, Mac OS X, and Linux variations. Next, click on the “Download Mullvad app” button to download the latest version. Select to save the installation file to your computer.
This page will also transfer you to the page where you can configure and copy the files you need to install OpenVPN and WireGuard on the devices that support it. We will see this when we examine Android installations later in our review.
Now that you have transferred the Mullvad app installation file, run it as admin to configure the app for your machine.
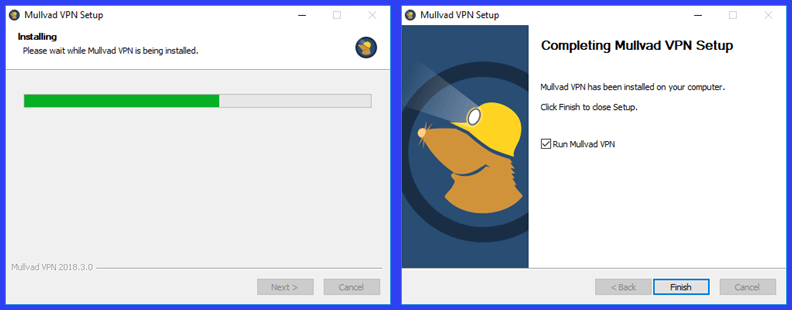
This installation completes without any input until the finish screen is displayed. Select the “Finish” button to open the Windows app for the first time. This will open the Mullvad VPN client’s login screen. Once this window opens, enter the “16 digit” number that was generated when you created your account. It is automatically saved when you login. Up to three of these numbers can be saved here. If you did not yet create an account, then select the “Create account” button to make one and return here to enter your account number. Once your account is verified, the app will open the main connection dashboard and log you into the last site visited.

By default, the app will initially connect to a server in Sweden. In this case it is a server in Malmö, Sweden. You may see a screen like the last one shown while the software finishes its connection process. Notice that it is blocking the Internet. This is an instance of the application of Mullvad’s built-in “kill switch”.
You will see this in a few different situations:
- if the app accidentally disconnects on its own
- if you run out of time on your account while connected
- while the app is establishing a connection when you start the app.
This is normal. By default, the app blocks all of your Internet traffic until a secure connection is made or reestablished, or until you manually disconnect from the client. This safety feature ensures that your online data is not accidentally leaked outside of the secure VPN tunnel.
Mullvad Windows Client Settings
Before we take a look at the Mullvad app in action, let us take a look at the settings that can be used to control its operation. You can access these by clicking on the gear icon in the upper right-hand side of the client dashboard. This opens the settings window.
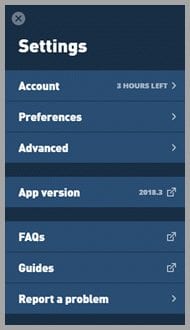
This window is divided into three sections. The first section has settings that allow you to control how the software behaves. The next opens the website download page so you can see if you have the latest version of the software. The last helps users find the support information they need. This includes links to the guides and FAQ pages on the Mullvad website, as well as, an in-client way to report software problems. Although not shown, there is also a button to quit the app at the bottom of the settings screen.
The first settings area is divided into three parts: account, preferences, and advanced. Account displays the time remaining on your subscription. It also lets you view your membership information. This includes your account number and when your paid time runs out. It also contains a link to their website to allow you to purchase more time. You can also log out of the software from here.
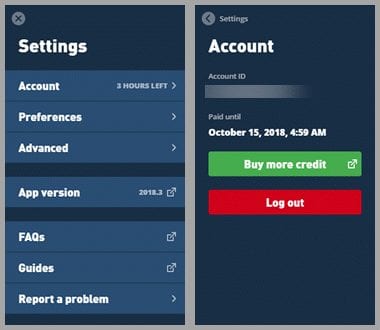
The next setting, Preferences includes startup options to auto-start and auto-connect to the VPN service when the system starts. It also lets you decide if you can use local network devices like printers while using the VPN. We recommend that you enable the auto-start and auto-connect to help ensure that your Internet traffic is always protected while online. You can decide about local network sharing but since sharing can cause security issues we recommend that you leave it disabled and print while offline.

The next option, Advanced allows you to determine how the software makes network connections. This is where you can enable/disable IPv6 communication and adjust settings for Network protocols, UDP ports, and TCP ports.
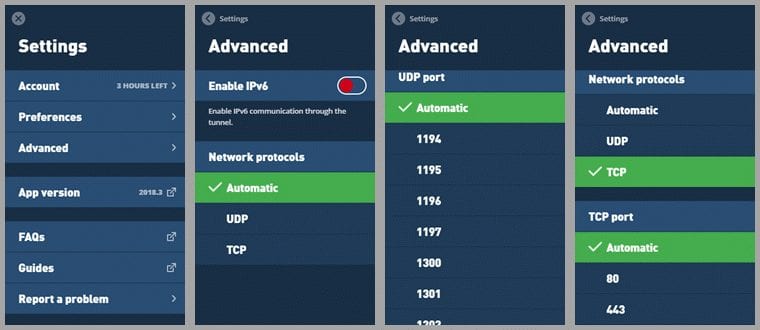
UDP is the default because it is generally faster than TCP. Therefore, we recommend that you use the defaults if you are not having any connection problems. You can also select between a number of UDP ports or let the app choose for you. However, you can use TCP if automatic or UDP connections fail. Once TCP is chosen, you can also choose to use either TCP port 80 (most often used by HTTP) or TCP port 443 (the standard port for HTTPS).
The last setting, report a problem opens a screen that allows you to report app issues from within the client. Your email address is optional. Include it if you need a response. You should also include a detailed description of the problem.
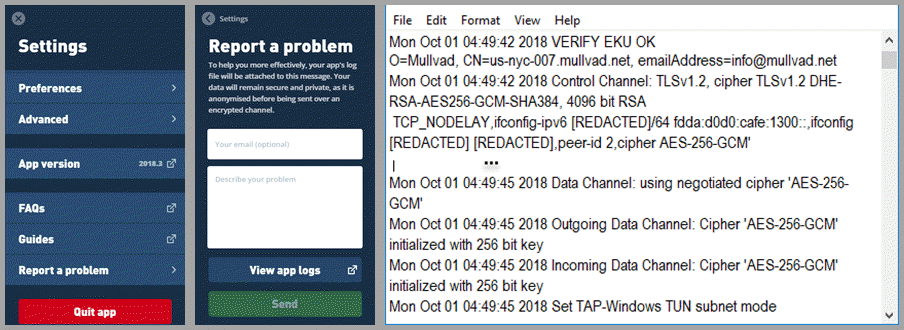
You can also examine and copy your log file from here. A copy of it will automatically be attached to the report so the support staff can effectively help you with any connection issues. Once completed, click “Send” and await their reply.
Using the Mullvad VPN Windows Client
Now that we have examined the software settings, let us look at it in action. If you will remember the app initially connected to Sweden when it first opened. This is shown on the main connection dashboard. Once the connection is complete, this screen displays a green background at the top and your virtual GPS location as a green dot on the map. It also shows “secure connection” in green text, lists your virtual location and IP address, and disconnect is shown on the action button.
Selecting “Switch location” opens the select location screen with the currently selected location checked and highlighted in green. Notice that Sweden is shown as the current location and not Malmö. This means that the software selected it for you. The app will automatically try to connect you to the best (closest and lowest load) server in the country that you choose.
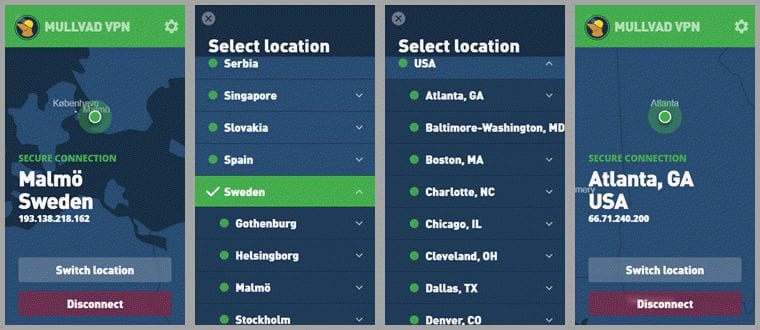
To change to a server in Atlanta, GA, simply scroll to USA and click on the down arrow beside it to expand its city locations. Then click on Atlanta, GA. The app will automatically disconnect from your current server and then point to the new virtual GPS location and then secure your connection to a server in Atlanta, GA.
You can not only choose the location (country, city) that you want to use but also the server as well. For example, suppose you now want to connect to the “us-nyc-007” server in New York City. Similarly to before, first click on the “Switch location” button. Notice Atlanta, Ga is our current virtual location.
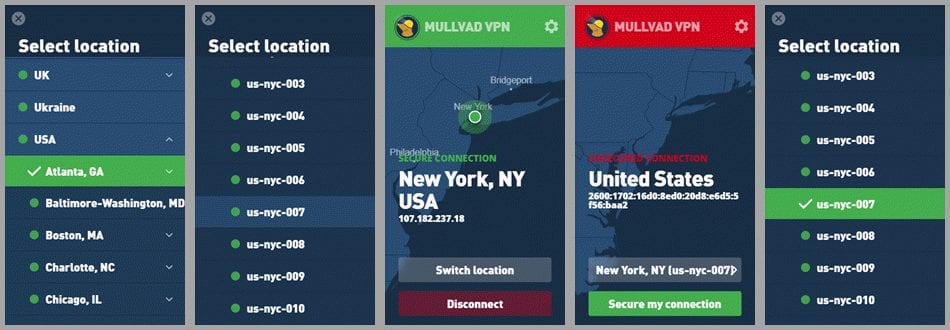
Since the USA country has already been expanded to city level, you can scroll to New York, NY, Once there expand it to open the list of servers. Finally click on the “us-nyc-007” server to finish changing your virtual location. If this fails, you can select “Secure my connection” to try again. Once the connection completes selecting switch location will verify that you are connected to the server you chose.
After you open the Mullvad app by clicking on its startup icon, it will open and then minimize to the system tray as a lock icon once it loses focus (you click outside of it). When unsecured it will appear as a open red lock. Clicking on this lock will allow you to use the dashboard to connect to the server in the location that you choose.
![]()
You may also see a “Mullvad VPN secured” connection message above the system tray area if the dashboard loses focus before the connection completes. The system tray now displays a closed green lock icon. This indicates that your Internet traffic is now secured by the Mullvad VPN service.
You may also see a green closed lock with a red dot in the center of it. This means that the app has activated the kill switch because of an unexpected VPN disconnect. This could be due to your account timing out or an interruption in the VPN connection.
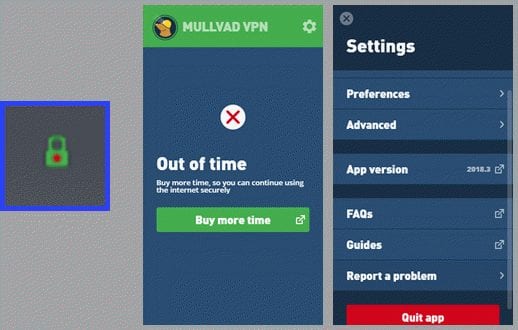
If this is the case and you need to access your Internet, you need to maximize the dashboard, open its settings menu, and click on the “Quit app” button. This will allow you to access your Internet once again.
Mullvad VPN Windows App Summary
The Mullvad VPN app for Windows is easy to install and use. It has a few basic settings that most users can just leave defaulted. However, if you need to change one it takes just a couple clicks to enable its toggle. When the app is opened, it will attempt to connect to the last connected location. Selecting a new location can be done at the country, city, and even individual server level on the select location screen. Simply scroll to the location you want and click on it.
Hands On: OpenVPN for Android
Once you have created a Mullvad account, you need to browse to their website on your Android device and tap on the “Download app” button in the website main menu at the top. After the next screen opens slide down to “iOS, Android, and other platforms”. Tap on the “Instructions and configuration files” button.
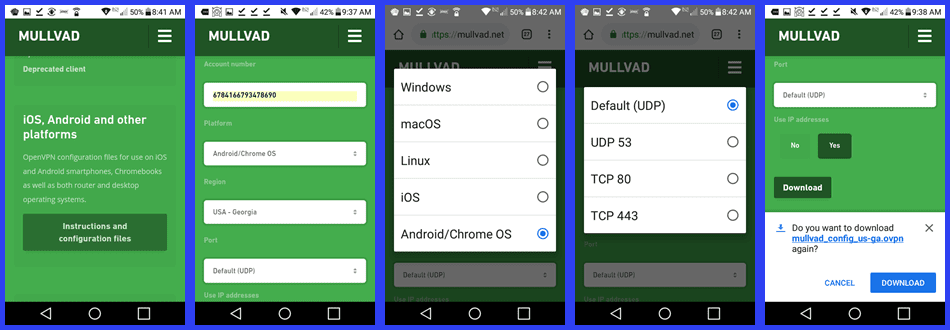
This opens the screen used to create and download the Mullvad .ovpn configuration files for the location(s) you want to use with your device. To complete this process follow these steps for each location you want to connect through.
- Enter your account number.
- Choose Android/Chome OS as the platform.
- Select USA-Georgia as your region.
- Go ahead and accept the default (UDP) port.
- Optionally select “Yes” to use IP addresses.
- Transfer the chosen configuration file to your Android device by tapping on the “Download” button.
- Repeat this procedure substituting USA-New York in step 3.
Now that you have Mullvad configuration files, you need to install OpenVPN for Android from the Google Play Store. Find the app and then tap on its “Install” button. After the app is installed, tap “Open” to start it on your Android phone. Its dashboard will open and inform you that no VPN profiles have been defined.
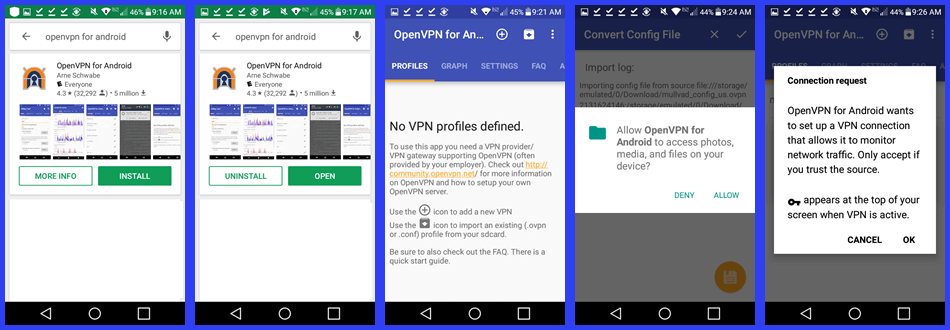
Tap on the + icon to add a new VPN. Allow the software the permission that it requires. Then tap “OK” to allow it to establish the VPN network.
Once a VPN network has been created, you need to add a Mullvad profile to connect to it. You can type a name for the profile or it will use the .ovpn file name. Tap import to convert the file and create the new profile.
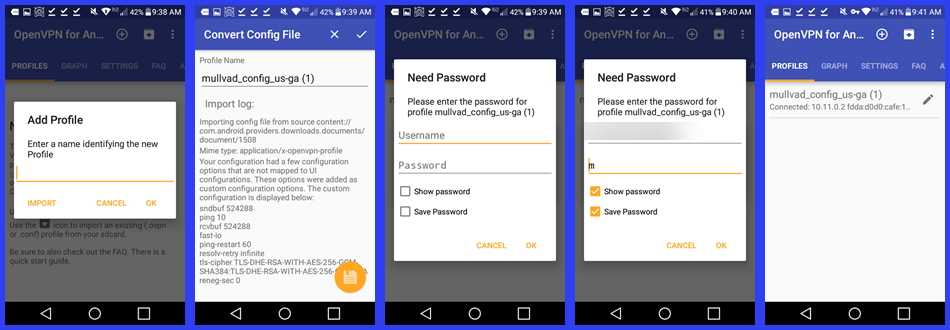
Before you connect to the new profile location, you need to authenticate it with the Mullvad VPN service. First enter your account number for the profile Username and “m” for the password. Finally, tap “OK” to complete the Mullvad Georgia profile and connect to it. The key that is shown in the notifications bar indicates that you successfully connect to the Mullvad VPN network and your Internet traffic is secure.
Select the add profile icon (circumscribed +) to create another profile for the New York Mullvad configuration file. Authenticate the new profile while creating it.
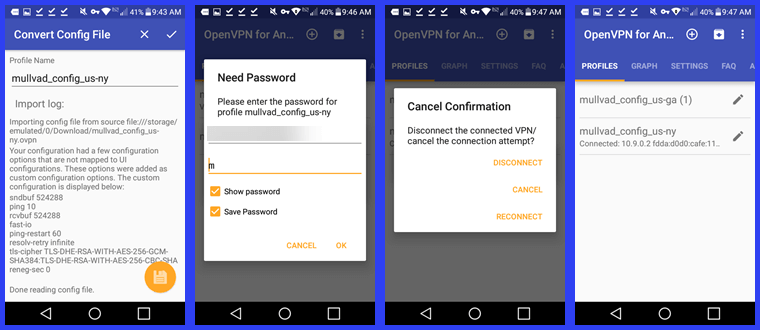
You can cancel your current connection by selecting it as was done for the us-ga profile above. Confirm that you want to leave the server by tapping on “Disconnect”. Then, tap on the new VPN profile (us-ny) that you want to use. Connection to the new Mullvad location is then completed.
Once you have successfully connected to a Mullvad server, you can examine the graphs of its bandwidth sent and received (kbit/s) versus time for the last five minutes, the average data transferred per minute, and the average transferred per hour. You can also look at these on a logarithmic scale. The settings used by the app can also be examined but changes are only saved when the service is not connected.
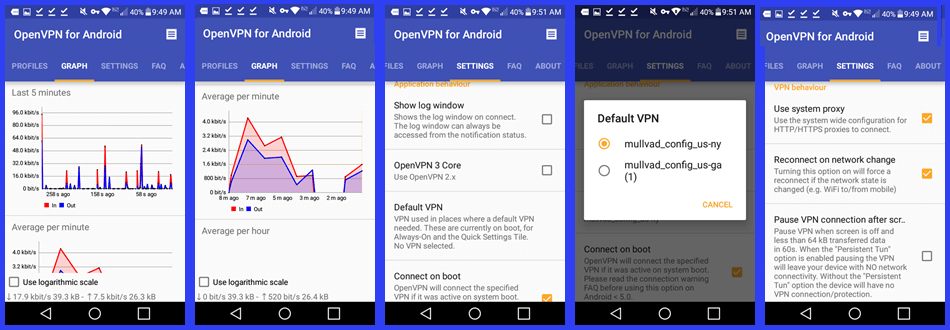
These settings are divided into two areas: application and VPN behaviors. The application behaviors include: show log on connect, use OpenVPN 3 core, and selecting a default VPN to automatically connect to on system boot. VPN behaviors include use system proxy, reconnect when the network changes (e.g. Wi-Fi to/from mobile), and pause VPN when not used for 60 seconds.
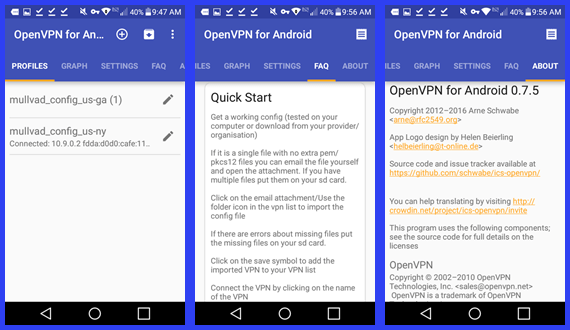
The other dashboard menu items is the profiles, built-in FAQ, and about versioning information. The profile screen lets you change between all installed profiles.
Mullvad on OpenVPN for Android Summary
Using the OpenVPN for Android to make connections to the Mullvad VPN service is easy but can be tedious if you have a lot of configurations that you want to connect to. Each configuration must first be created and downloaded. Then they have to be individually converted to profiles using OpenVPN for Android. This includes authenticating each profile with the Mullvad VPN service.
Hands-On: Connecting to Android with WireGuard
WireGuard secure tunnels can also be used to connect to the Mullvad VPN network from your Android device. Once you have an account number, you can use it to generate a public/private key pair. After you enter your account number, you have three options for key generation:
- Generate new key pair – will create a new pair in your browser. The public key is sent to Mullvad. They will use it to assign an IP address to you and grant you access to their WireGuard VPN servers.
- Reuse last key pair – will simply reuse the last key pair that you generated in this browser session and use it for new configuration files.
- Custom key pair – allows you to retrieve a key pair from a previous generated one by entering its associated private key.
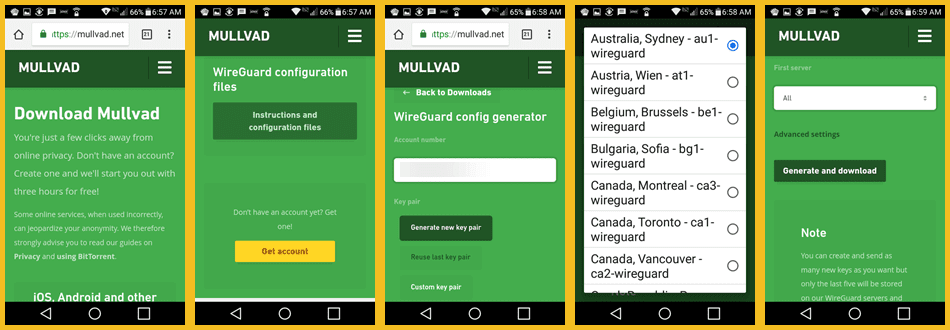
You then select the server that you want to connect to with WireGuard. You can select “All” if you want to copy all servers at once. Then, tap on the “Generate and download ” button to complete the transfer of the Mullvad configuration files.
Once the configuration files are on your Android phone or tablet, you need to install the WireGuard Android app from the Google Play Store. This is an unreleased beta version which operates at the user level. First open the store and search for the WireGuard app. After the app is found, tap on its “Install” button. After the installation completes tap “Open” to start it up on your device.
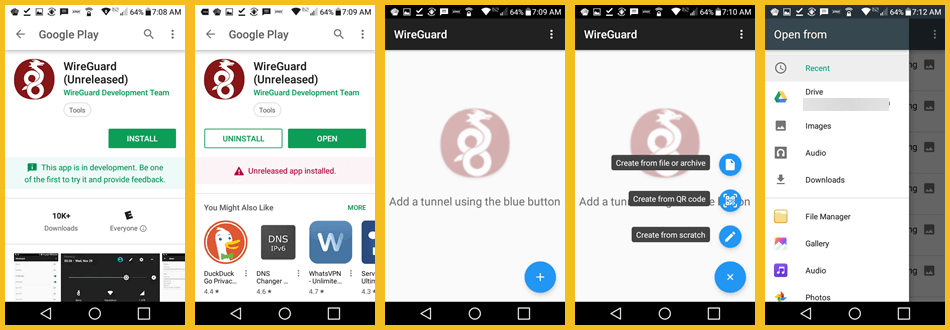
This will open the WireGuard app and let you add secure tunnels. Tap on the blue button and begin adding VPN tunnels. There are three different ways that you can do this.
- Create them from a file or archive.
- Use a QR code to create them.
- Create them from scratch.
Select “create from a file or archive” and then open the downloads folder where the zip file that contains all of the Mullvad VPN configurations are stored. Tap on the mullvad-wireguard-configs zip file to unzip it. This creates toggles for each server network interface (secure tunnel).
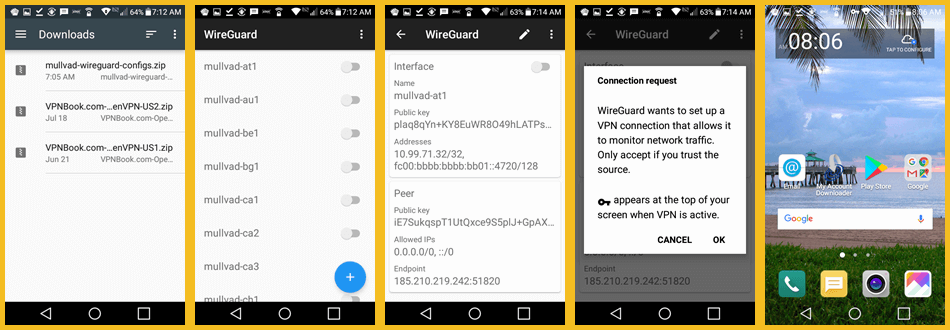
Tapping on a WireGuard Tunnel will display its interface with client and peer public keys, associated addresses, and last known endpoints. The peer represents the server in this instance. Toggling your first interface on results in the usual VPN establishment permission screen. Tap “OK”. Successful secure tunnel connections are indicated by the key icon at the top of your screen. To connect to a new VPN interface, you must first toggle your current one off. Then you can select another location to connect to.
Mullvad on WireGuard for Android Summary
After you have created a Mullvad account, you have to generate a set of public/private keys. The private key is stored on your device and the public key is sent to Mullvad. They use it to assign you a valid IP address for their service. Next, choose the location(s) that you want to setup. You can select all to create a zip file containing all of them. Finally, generate the config file and download it to your Android phone.
Next, you have to install the WireGuard app for Android from the Google Play Store. Finally use the WireGuard app to open the zipped Mullvad configurations file and create the WireGuard secure tunnel interfaces. After this, connecting to a tunnel takes only a tap or two. Remember to toggle the current interface tunnel off before you can choose another.
Mullvad VPN Speedtest
We tested the Mullvad for Windows app which uses the OpenVPN (UDP) protocol with AES-256 encryption. The service performed well on our speed tests. We were pleased with its overall performance. The small loss of speed is due to the encryption overhead that their encryption algorithm incurs.
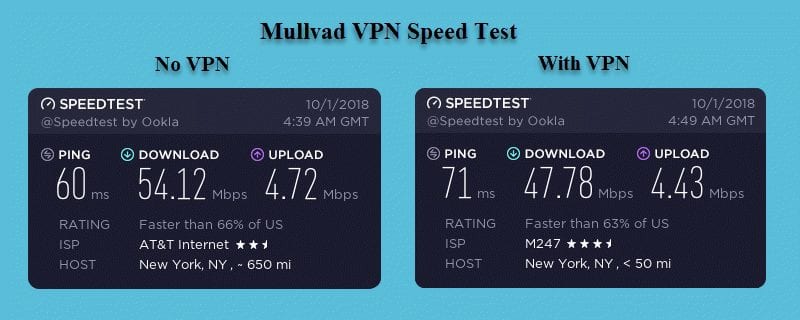
You can see that our download speed was 54.12 Mbps without the VPN connection but decreased to 47.78 Mbps when using the Mullvad VPN server. This is a drop of about 11.7% to a server in New York City, NY. We found similar results when using other locations. There was a 5.7% loss to a server in Atlanta, GA and 26.4% to a server in Sydney, AU. As expected, more speed loss is observed as distance and ping times are increased. Even with this loss in speed, the 40+ Mbps speeds is still fast enough for most applications that you might want to use a VPN with. You may have different results in your region of the world.
Mullvad VPN Review : Conclusion
Mullvad has been in the VPN industry for about ten years. Their headquarters is in Sweden which is part of the “14 eyes” network. As a result, Mullvad goes out of its way to help keep you more anonymous. This starts with account creation. Mullvad accounts do not require email addresses, names, or any other personal information. Instead, accounts and resources are authenticated and managed by randomly generated “16 digit” numbers. Additionally, they accept anonymous cash and Bitcoin payments to subscribe to their VPN service.
Mullvad initiated an extensive upgrade of their VPN service a couple of years ago. Since that time, they have increased both the coverage and performance of their network architecture. Mullvad accomplished this by upgrading the bandwidth of their primary servers, and adding servers to more locations and regions. They own their servers in both Sweden and the Netherlands. Physical servers from Tier 1 or Tier 2 providers form the backbone of their service. These servers are not shared with others.
They currently have a mid-sized network with over 60 locations in 30 different countries. It contains three different types of servers: OpenVPN, WireGuard, and bridge servers. Mullvad has about 260 OpenVPN severs, 48 WireGuard servers and 6 bridge servers. They have servers in Asia, Europe, North America, South America, and Oceania. Their VPN service allows P2P traffic and they offer guides to help you use it more efficiently on their VPN servers.
The Mullvad service only allows connections through OpenVPN and WireGuard. They have a custom OpenVPN app for Windows, Mac OS X, and multiple Linux variants. OpenVPN configuation files (.opvn) are also available to manually install and use it on devices that support it like the iPhone and iPad. They have guides to help you set these up on their website.
Mullvad is also an early adopter of the VPN infrastructure WireGuard. They allow connections through Linux and Android devices (Android is a Beta) to their WireGuard servers. WireGuard began as an open-source Linux kernel add-on, but is undergoing major development to port it to other operating systems. It is touted by many as the “heir apparent” to OpenVPN.
Mullvad secures their OpenVPN connections with AES-256. They provide forward secrecy and use RSA-4096 for handshakes. They do not collect or store any logs of your Internet activity, bandwidth use, or DNS queries. Their service provides DNS, IPv4, and IPv6 leak protection. Their support is primarily through email tickets. Additionally, they have a FAQ database and guides to install their service on a variety of devices with both OpenVPN and WireGuard.
What we liked about the service:
- You can create an anonymous account by paying with Bitcoin or cash.
- They do not keep VPN activity logs.
- The service provides excellent security for OpenVPN connections.
- Each account can have five simultaneous connections.
- They are an early adopter of WireGuard and believe in open-source software.
- They allow P2P on their network servers and they have guides to help you use it more securely.
- Mullvad offers a 30-day money back guarantee for some payment methods.
Ideas to improve the service:
- Add live chat and some form of 24/7 support.
- Develop a custom app for mobile devices.
Mullvad has servers in Asia, Europe, North America, South America, and Oceania. They offer a reasonable monthly price. In addition they have a 30-day money-back guarantee for some payment methods. This means you can try out their VPN service with minimal risk. If you decide you like it you can get full access to their network for €5 per month.