![]()
![]()
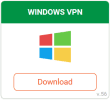
You can now click on your shortcut to run the client. The first time you open it, you will see a verification and login page similar to the one shown on the right below.
- Start application at login – This will start the client when you log into Windows.
- Auto-Connect when app is started – Auto-connect to your chosen location when the Client starts up.
- Region – This allows you to choose a country you want to auto-connect to. If set to auto, it will connect you to the fastest server from your current location.
Once you have set these basic options, then click the “Save” button and the client will finish launching. We will discuss the advanced options later in this section. The client does not have a fancy user interface. It simply loads into the system tray and looks as follows.


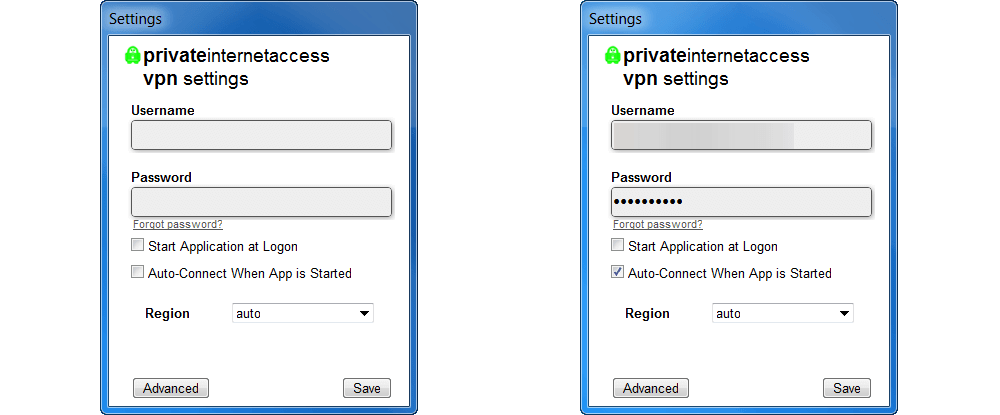
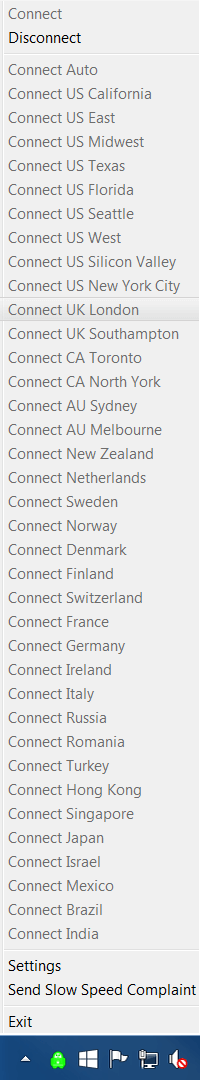
Hovering the mouse over the client in the tray or taskbar area will show you your current connection. Right-clicking on the client icon will open a list of servers for you to connect to as is shown to the right of this text.
We are currently connected to a server in UK London. Note, the virtual IP from that location is also shown but has been redacted in the image above. To change VPN servers, you must first disconnect from the current London server by clicking “Disconnect” at the top of the list. Notice that all other locations and “Connect” are greyed out and not selectable till you disconnect from the London server. This will close the location list and the client icon will turn red indicating that you are no longer connected as is shown in the image below.


There are a few more list items in the PIA client shown above right. The last list item “Exit” will shut down the client. The second, “Send Slow Speed Complaint” will let the staff at Private Internet Access know that they have a problem that needs to be examined. The first is “Settings” which will open a window like the one shown below-left. If it looks familiar, that is because it is the same login screen we saw earlier in this section. We are now going to take an in-depth look at the advanced features that the PIA client offers.
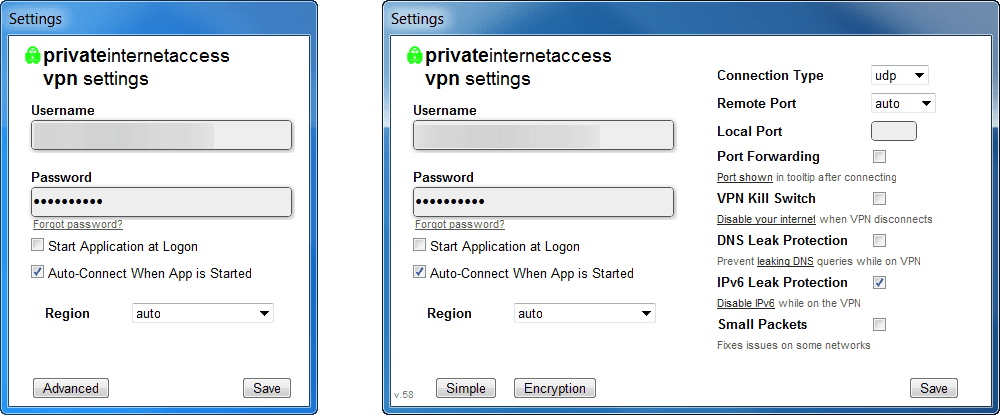
Clicking on the “Advanced” button results in a screen like the one on the right which has been expanded to show the advanced connection settings. Clicking on the “Simple” button will close the advanced settings and return you to the screen shown on the left above. The advanced connection settings are as follows:
- Connection type – Their are two types of connections possible with the OpenVPN protocol over IP.
- UDP – This is the User Datagram Protocol which is used with low latency connection and loss tolerating ones. This is the default OpenVPN protocol for the client and best for most users. Does not have to check for packet order or loss.
- TCP – This is the Transfer Control Protocol and is good for high latency connections and those which cannot tolerate loss. It provides error checking for packet order and loss and resends packets to correct. This is usually slower because of the extra overhead involved in this process.
- Remote Port – This lets you choose the remote port to tunnel data through.
- Port 1194 – This is the standard OpenVPN port for both UDP and TCP.
- Port 8080 – This is the alternative port to Port 80 for HTTP web services. It is commonly used as a proxy port.
- Port 9201 – This is the port used for WAP (Wireless Application Protocol) services on mobile devices.
- Port 53 – This is the port used by DNS.
- Local port – This allows you to set a local port to route through the remote port.
- Port forwarding – Turning this on allows you to set up an application which allows remote users to connect to it. The remote users must know the device name and port to successfully connect to it.
- Port forwarding is only through the following gateways: CA Toronto, CA North York, Netherlands, Sweden, Switzerland, France, Germany, Russia, Romania, and Israel.
- After enabling port forwarding and re-connecting, hover the mouse over the system tray icon to see the port number to put in your application.
- VPN kill switch – Once set, this will kill all Internet traffic from the device if the VPN connection is dropped.
- It will restore Internet traffic once the connection is re-established.
- Disabling this switch or exiting the VPN client will also restore normal Internet access.
- DNS leak protection – This ensures that all DNS request are routed through the VPN which will provide you with the greatest level of privacy.
- IPv6 leak protection – This disables a IPv6 request while using the VPN.
- Small packets – This transfers the data in smaller packets which can fix some network issues.
The links shown under port forwarding, VPN kill switch, DNS leak protection and IPv6 leak protection will take you to guides on the Private Internet Access website which contain more detailed imformation about that particular setting. Clicking on the “Encryption” button in the image on the right above will bring up the encryption options in place of the connection settings as shown in the image below.
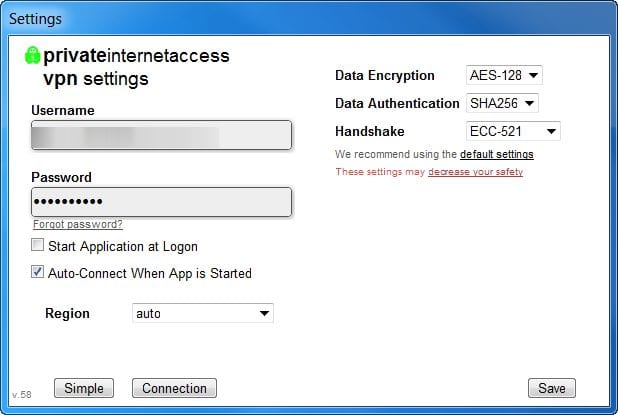
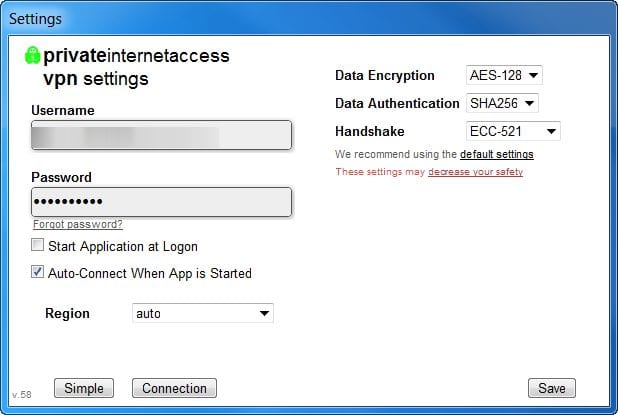
The encryption panel consists of the following settings:
- Data Encryption – This is the encryption used to encrypt and decrypt all of your Internet traffic once the initial encrypted tunnel has been established.
- AES-128 – Advanced Encryption Standard (AES) is the National Institute of Standards and Technology (NIST) chosen protocol and the one used by the United States government for secret documents. This one uses a AES-128 CBC (Cipher Block Chaining) with a 128 bit key and will provide the best performance for most uses.
- AES-256 – This uses the same encryption algorithm as above. AES-256 CBC uses a 256 bit key, thus is more secure and slower.
- Blowfish – This uses Blowfish-128 CBC with a 128 bit key as an alternate to AES. This is a secure algorithm and was one of the runner-ups in the NIST standards competition.
- None – This does not encrypt your data and is not recommended as it only hides you IP and thus means the VPN is being used as a pseudo proxy. You will be susceptible to passive attacks where your data is recorded by a third party without your knowledge. This can help you overcome geo-restrictions.
- Data Authentication – This refers to the algorithm that authenticates all of your data to guard against active attacks (attack where an entity adds or removes packets from your message).
- SHA1 – This uses HMAC (Key-Hash Message Authentication Code) with a 160 bit key.
- SHA256 – This utilizes HMAC with a 256 bit key and is thus slower.
- None – This opens you up for active attacks or Man-in-the-Middle (MitM) from outside sources where the attacker intercepts your message and alters it before sending it on the VPN server.
- Handshake – This is the algorithm which establishes the initial secure connection and verifies that you are talking to a PIA Server and not an imposter. Hence the name handshake. Private Internet Access uses Transport Secure Layer v1.2 (TSL 1.2) for this connection and all certificates are signed using SHA512.
- RSA-2048 – This uses a 2048 bit Ephemeral Diffie-Hellman (DH) key exchange and 2048bit RSA certificate for verification.
- RSA-3072 – This uses the same algorithm as above with 3072 bit for both key exchange and RSA certificate.
- RSA-4096 – This uses the same algorithm as above with 4096 bit for both key exchange and RSA certificate.
- ECC-256k1 — Ephemeral Elliptic Curve DH key exchange and an Elliptic Curve Digital Signature Algorithm (ECDSA) certificate for verification. Curve secp256k1 (256bit) which is the curve that Bitcoin uses for its transactions and is used for both the key exchange and the certificate.
- ECC-256r1 — Like above but curve prime256v1 (256 bit, also known as secp256r1) is used for both the key exchange and certificate used for verification.
- ECC-521 — Like above but curve secp521r1 (521 bit) is used for both the key exchange and certificate verification.
You will receive a warning like we did in the above image if you select none for data encryption, none for data authentication, or one of the ECC handshake algorithms. The Private Internet Access client defaults to AES-128/SHA1/RSA-2048 which should provide the best balance of performance and security for most users. Clicking on the “default settings” link will open the VPN encryption page on their website and take you there. Clicking on the “decrease your safety” will also take you to their VPN encryption page and explain more about why you should not use the settings you have chosen.
Here are some endpoint encryption settings along with some comments about them.
- Maximum Protection – AES-256/SHA256/RSA-4096: This is for those who want the maximum security for their data and can accept the extra speed loss.
- Default Recommended Protection – AES-128/SHA1/RSA-2048: This provides the best balance of speed and protection and thus the desired setting for most users.
- Risky – AES-128/None/RSA-2048: This configuration is suceptible to active MitM attacks.
- All Speed No Safety – None/None/ECC-256k1: This is suceptible to both active and passive attacks from outside third parties (hackers). You might as well not have a VPN as only your IP is hidden.
The Private Internet Access client may not be the prettiest client in the field today but it offers some of the most advanced features that VPNs have today like a kill switch, DNS leak protection, disabling IPv4 Internet traffic, and small packets. This makes it appealing to those users who have more technical knowledge. At the same time it has a simple mode which uses default settings. This is probably best for most users. All that is necessary to connect to a one of their VPN servers is to select its location from the list that appears when you right click on the client icon in the system tray area. If the icon is green, you are safely connected and if it is red you are not. It does not get much simpler than that.

